In this blog, we dive into the world of Android app security by exploring exported activities and intent filters. These components, defined in the AndroidManifest.xml file, allow apps to interact with each other but can also expose your app to serious security risks if not properly configured. Learn how to identify exported activities, analyze intent filters, and understand the potential vulnerabilities they introduce.
In our latest blog, we take a closer look at the manifest file of Diva.apk, revealing potential issues that could put user security at risk. We discuss permissions for external storage access and the concerning presence of debug mode, pointing out key problems developers need to fix…
Learn how to perform static testing on Android applications to identify vulnerabilities, hardcoded secrets, and insecure configurations. Explore tools, steps, and best practices for secure app development.
Setting up a dedicated lab is your first step towards uncovering the vulnerabilities of Android applications in a safe and ethical manner.
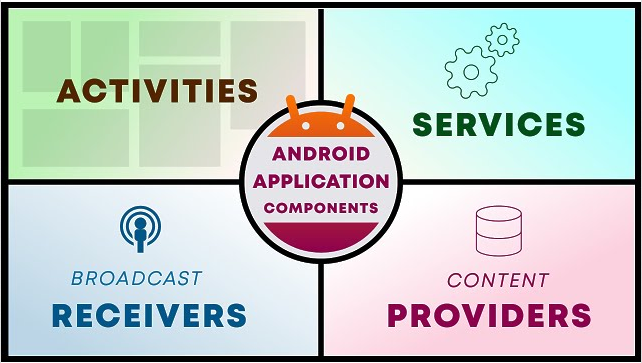
Android applications are built using four main components, each with a unique role in the app’s functionality….
Dive into the world of Android penetration testing, where the intricacies of the kernel and OS architecture come to life! Discover how the layered architecture—from the Linux kernel to the applications layer